
The Society for Worldwide Interbank Financial Telecommunication (SWIFT) provides secure global payment services worldwide. In 2017, it launched the Customer Security Programme (CSP) as a targeted measure to combat cyberattacks. For 2020 the CSP has been further expanded and the assessment process has been tightened.
Today, SWIFT manages the communication traffic and transactions of more than 10,000 banks, insurance companies and corporates worldwide through its secure, standardised telecommunication network. The growing number of cyberattacks on the SWIFT network participants’ infrastructure and therefore on the SWIFT network has prompted the transactions specialist to develop a security programme for its participants. With the CSP, it intends to harness the collective strength of network participants to counter threats from cyberspace.
The CSP was launched in 2017. It defines requirements for all participants with the aim of improving the exchange of information within the SWIFT community and maintaining an appropriate level of security for participants’ local SWIFT infrastructure. With this framework for coordinated quality assurance, SWIFT is aiming to counter rising cyber risks and bolster the defensive capabilities of SWIFT participants against cyberattacks.
SWIFT attestation rate for CSCF 2019
As stated in the SWIFT Customer Security Programme update of March 2020, more than 91% of all SWIFT customers, representing over 99% of SWIFT’s traffic, have attested to their compliance with controls mandated by SWIFT’s Customer Security Controls Framework (CSCF). Furthermore, SWIFT states that for those customers that did not attest or did not fully comply with all of the mandatory controls, SWIFT reserves the right to report the customer to their local regulator.
Tightening of the programme
Every year, SWIFT adapts its security programme to current circumstances. For 2020 it has upgraded two previously advisory-level controls to mandatory controls and added two new advisory controls to the programme (see Figure 1). In addition, existing individual controls have been substantiated.
SWIFT released its new CSP version on 17 July 2019. Participating financial institutions must demonstrate to SWIFT that they are in compliance with all mandatory controls by the end of 2020.
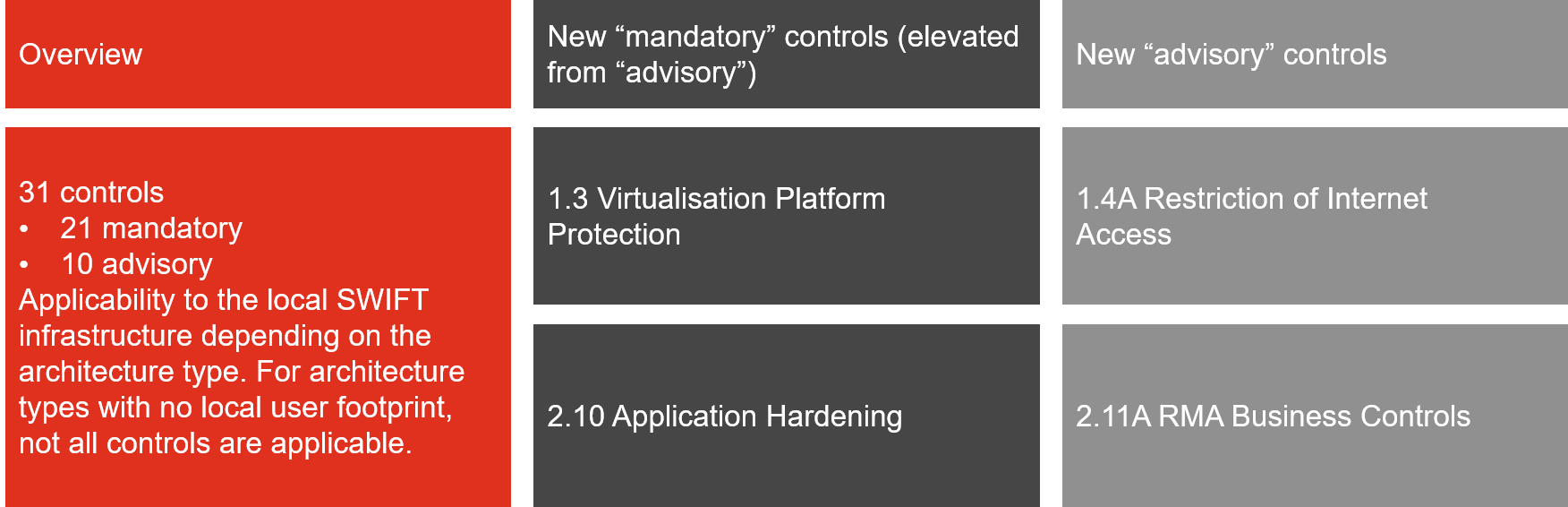
Figure 1: Overview of key CSP updates for 2020
Substantial changes to the attestation process
In contrast to the previous versions of the CSCF, a “user-initiated assessment” (self-assessment) can no longer be carried out under the new CSCF version 2020. From now on, only independent assessments are permitted, according to the “Community Standard”, which can be carried out by external assessors or, if the relevant specialist skills are available, by the internal audit department. If independence is ensured, it is also possible to have such an assessment carried out by the second line of defence (e.g. risk control, CISO).
For quality assurance reasons, SWIFT will also require an independent external assessment (“SWIFT-mandated assessment”) for a selection of participants.
Implementation with far-reaching consequences
Experience from the attestation cycles has shown that implementing the security programme and complying with the CSP requirements on an ongoing basis require great effort on the part of SWIFT participants. This is because SWIFT’s requirements are extensive and also cover the participants’ local IT infrastructure. In addition, individual requirements for some SWIFT participants go beyond the in-house requirements for solid basic protection.
SWIFT participants asked and challenged
The latest changes and innovations in the CSP represent much more than small adjustments in the security system for financial institutions in the SWIFT network. They have to secure the operational effectiveness of the controls implemented and thus their SWIFT compliance. This means that they should deal comprehensively with the upgraded and new mandatory controls early on. It is worth reading the detailed description of the CSP content on the SWIFT website, since the new requirements may not have been taken into account for the local security architecture. This means that SWIFT participants may have to implement new control measures and check their effectiveness - and soon.
Furthermore, SWIFT participants are well advised to determine the type of attestation in good time due to the changed verification process (internal/external). In the event that a previous self-assessment is replaced by an external assessment, it is essential to find the right partner and get them on board at an early stage.
External assessment as a farsighted solution
Adequate implementation of the SWIFT requirements can be demonstrated more easily with a structured procedure. At PwC we work in various roles for a range of SWIFT participants (see Table 1). We help SWIFT network participants to ensure that their information and cybersecurity comply with the rules, particularly under time pressure, and to refine their SWIFT compliance in a targeted manner.









