
Most financial institutions implemented robust processes to manage IT and cyber risks. Some improvements are possible, notably regarding cyberattack detection and incident response.
Based on our benchmark, the main weaknesses in the way financial institutions manage their cyber risks are the following:
- Implementation of security measures is not always linked to actual threats identified through a proper cyber risk assessment process
- Existing processes and tools overemphasise protection at the expense of detection and response
- A fair share of financial institutions still don’t adhere to the Swiss Banking Association’s recommendations for business continuity management, dated 2013
As a result, we are of the opinion that financial institutions need to better balance their effort across all dimensions of cyber security from strategy to identification and protection to detection and response to recovery.
Background
In September 2016, FINMA revised its circular 2008/21 ‘Operational Risks’. The changes included tighter requirements regarding IT and cyber risk management for financial institutions (FIs). FINMA requested the institutions’ external auditors to confirm the implementation of the FI’s IT and cyber risk management concepts, which had to be in place as of 1 July 2017.
Results of our benchmark of IT and cyber risk management concepts
PwC Switzerland has assessed the maturity levels of the following seven requirements taken from Principle 4 of FINMA circular 2008/21 ‘Operational Risks’ and relating to IT and cyber risks:
- IT risk management: Executive management shall ensure that an IT risk management concept is implemented;
- Cyber risk – strategy and policies: Executive management shall implement a risk management concept for the handling of cyber risks that addresses at least the following five requirements and shall define the roles and responsibilities in this context;
- Cyber risk – identify: FIs shall identify potential threats resulting from cyberattacks;
- Cyber risk – protect: Executive management shall protect business processes and IT infrastructures against cyberattacks;
- Cyber risk – detect: FIs shall rapidly identify and detect cyberattacks based on systematic monitoring processes;
- Cyber risk – respond: FIs shall react to cyberattacks in a timely manner using targeted measures;
- Cyber risk – recover: FIs shall guarantee the timely recovery of business processes and IT infrastructure after a successful cyberattack.
We have consolidated and anonymised our assessments to create a benchmark describing the status of the FIs in terms of conformity with FINMA's requirements. We have also gathered information on the security tools and risk scenarios considered by the FIs included in the benchmark panel.
Our assessments are based on professional judgement rather than on quantifiable and objective data; consequently, they are subjective. The results presented here are based on the assessment of a panel of 114 banks and 8 security dealers in Switzerland broken down nationally as follows:
- French-speaking Switzerland: 24%
- German-speaking Switzerland: 71%
- Italian-speaking Switzerland: 5%
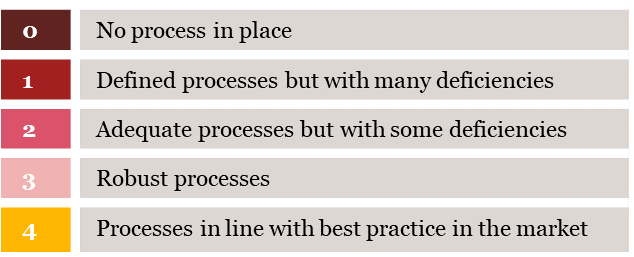
The scale we apply is as follows:
| 4 | Processes are in line with best practice in the market |
| 3 | Processes are robust |
| 2 | Processes are adequate with some deficiencies |
| 1 | Processes are defined but with many deficiencies |
| 0 | No process are in place |
In order to comply with FINMA’s requirements, FIs must have robust processes (rating 3) or processes aligned with best practices (rating 4).
We have classified the seven requirements covered by Principle 4 of FINMA circular 2008/21 ‘Operational Risks’ from the most mature to the least mature.

Classification of principles from best implemented to least mature
Scales applied
Key highlights
A strong basis in IT risk management (‘IT risk management’)
Of the benchmark panel, 93% have IT risk management processes that are at least ‘robust’ or ‘aligned with best practices’. This high rate is the result of FIs having worked to improve their IT risk management processes over the last three years in response to FINMA’s increased scrutiny of risk management.
Is the cyber security strategy aligned with cyber risks? (‘Cyber risk – strategy and policies’, ‘Cyber risk – identification’)
We note that 24% of the panel demonstrate insufficient maturity with regard to the implementation of a cyber risk management concept (‘Cyber risk – strategy’) and the identification of potential threats resulting from cyberattacks (‘Cyber risk – identification’). On the basis of our figures, we conclude that the cyber defences of the companies concerned might not be adequately aligned with the cyber risks they face, which could lead to the implementation of unsuitable controls and security measures.
Major investments in security solutions (‘Cyber risk – protect’, ‘Cyber risk – detect’)
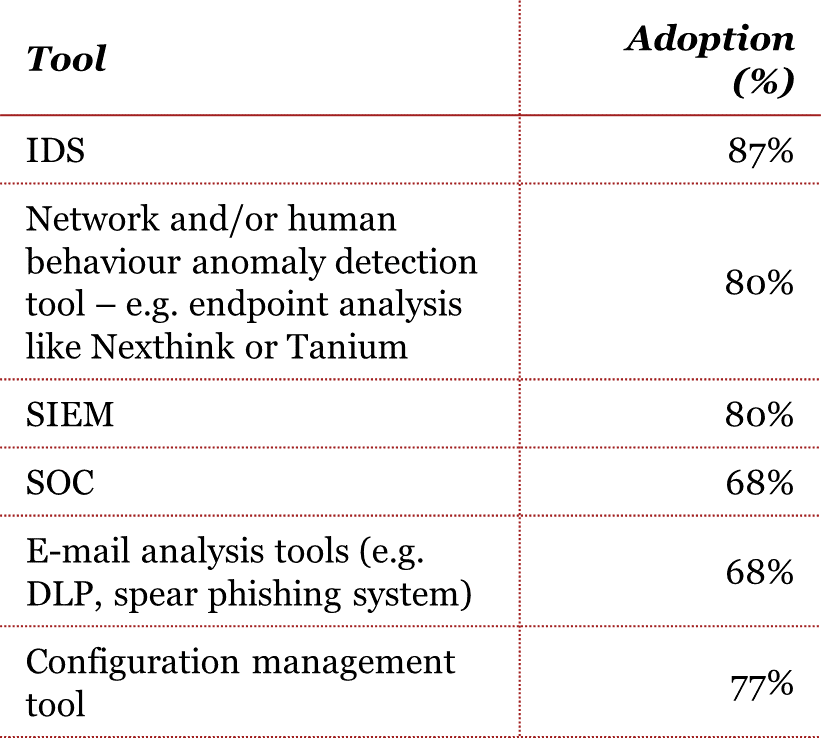
The benchmark highlights the high rate of adoption of security tools. It is important to note that we use the word ‘adoption’ and not ‘implementation’ as our benchmark is based on professional judgement rather than quantifiable and objective data.
Over the years, FIs have invested significantly in technical solutions to protect their information assets and infrastructure, which explains the high percentage of participants with at least ‘robust’ processes (83%).
Aside from standard network-based security equipment (e.g. IDS), there is a trend towards the adoption of increasingly advanced technologies for the purposes of security alerting (e.g. behaviour analysis, SIEM, DLP, SOC, etc.). These support more efficiently the cyber risk detection function (‘Cyber risk – detect’) of information se curity, where the benchmark currently reveals a lack of maturity. Actually, 19% of the benchmark participants are not fully compliant with the FINMA requirements in this domain.
It is interesting to note, too, that 68% of the panel have adopted or intend to adopt an internal or external security operations centre (SOC). This high rate of (potential) adoption highlights that participants understand the growing complexity of cyber risks and the need to structure their defence and detection capabilities to cope with cyber threats.
Benchmark highlights
Are FIs able to respond to cyberattacks and recover from them? (‘Cyber risk – respond’ and ‘Cyber risk – recover’)
Over the last two years, we have seen that FIs are training their people to deal with cyberattacks and, in some cases, conducting tabletop exercises. This is reflected in our survey by the 82% of the FIs that comply with FINMA’s requirements in this regard.
Most of the benchmark participants have a mature Business Continuity Plan (BCP) in place, based on the recommendations of the Swiss Banking Association (SBA). These BCPs have been adapted to consider the recovery activities that follow a cyberattack. However, we note that 17% of the FIs still have work to do, as they are not fully compliant with the requirements.
What are the FIs’ main concerns?
As demonstrated by recent events, malware is now a major factor in cyberattacks. Malware may lead to major dysfunctions, including data loss. This is clearly a key concern for the FIs (89% of the FIs consider it a key threat) together with the risk of data leakage (also considered a key threat by 89% of FIs).
It should be noted that –¬ even in the wake of digital banking – the FIs on the panel are less concerned by threats that could affect their mobile or online presence (although this is certainly influenced by the number of private banks in the benchmarked population). As FIs deploy new digital services to their clients, these additional potential threats should be considered thoroughly in any new risk analysis, and the risk profiles and related controls environments updated accordingly.
Recommended actions
Based on the results of our benchmark, we would recommend the following actions to FIs.
1. Align your cyber risk strategy with your cyber risks and align cyber risk management with your overall risk management framework
FINMA developed its requirements based on the NIST framework, which is also used by the Federal Office for National Economic Supply (FONES).
The NIST framework is based on a ‘virtuous circle’. In order to ensure a consistent cyber security strategy, companies need to understand and assess their particular risks depending on their environment. Once those cyber risks are identified and assessed, companies have to recognise which controls (people, process, technology) can address those risks. Finally, management must accept the residual risks. Without proper and effective cyber risk management, companies could face not only a serious impact on their resilience, but also run the risk of making the wrong investments.
2. Reallocate your budgets from protection to detection and response
Today, we can say that cyberattacks have become part of the ‘new normal’ of our digitally connected world. Consequently, FIs need to reallocate information security budgets more into rapid detection and response approaches, rather than focusing on protection. We would also recommend that FIs periodically check their cyber resilience by organising tests of their BCM in the light of a cyberattack.
How PwC can help you
As a multi-disciplinary practice, we are uniquely placed to help you adjust to the changing regulatory environment. We have developed a range of proprietary tools covering breach detection, intrusion analysis, event correlation and threat intelligence. Based on these capabilities and on our strong expertise in regulations, we have designed a dedicated service to help you cope with forthcoming regulatory challenges.
Our service offering comprises an overall assessment of your cyberattack readiness as well as targeted initiatives designed to respond to each of FINMA’s requirements relating to cyber risk management.







